Introduction
EasyLAPS is a tool designed to regularly rotate the password of the local administrator account on a Mac and store it securely in either a Mobile Device Management (MDM) solution or a Password Management solution. Its primary purpose is to ensure that each Mac in the fleet has a unique, regularly updated password, centrally accessible through the chosen escrow service.
EasyLAPS offers two functioning logics and is designed to manage transparently a change between the two.
Logic #1 — The password is stored in encrypted form in the escrow service and in the EasyLAPS Keychain. EasyLAPS uses the locally stored password as the current password to manage the rotation to the new generated one which is then written in the escrow service. The public key used for the encryption is part of the EasyLAPS configuration file. The private key is not present on the device and must be kept in restricted access. This logic fits best when a large number of technicians have access to the escrow service console and only those who own a copy of the EasyLAPS-Toolkit with the private key can reveal a rotated password.
Logic #2 — The password is stored in clear text in the escrow service and is not stored locally unless a password reversion fails. EasyLAPS reads the password stored in the escrow service and uses it as the current password to manage the rotation to the new generated one which is then written in the escrow service. The logic fits best when a restricted number of technicians have access to the escrow service console and then are able to reveal a rotated password.
After the first successful rotation, the new password is visible in the device inventory record.
EasyLAPS operates a true rotation of the local administrator password, so the account keeps its cryptographic status. That means that once the password is changed, the account is still a Crypto user and Volume owner, able to unlock the device, install macOS updates, make changes to the startup security policy, initiate an Erase All Content and Settings, and more.
Screenshots
Microsoft Azure Key Vault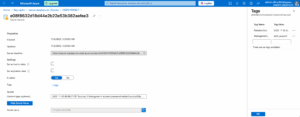
Enlarge
Passwordstate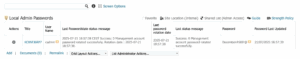 Enlarge
Enlarge
Omnissa Workspace ONE UEM  Enlarge
Enlarge
Microsoft Intune 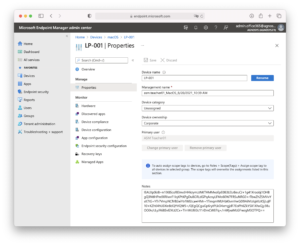 Enlarge
Enlarge
Jamf Pro 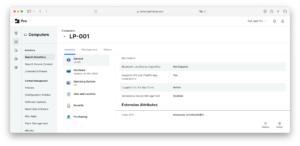 Enlarge
Enlarge
Jamf School 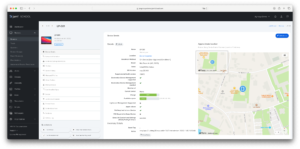 Enlarge
Enlarge
SimpleMDM 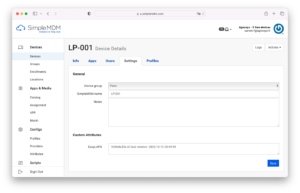 Enlarge
Enlarge
FileWave  Enlarge
Enlarge
JumpCloud 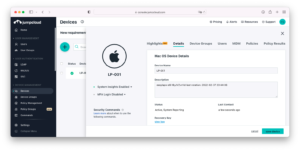 Enlarge
Enlarge
Mosyle Business Enlarge
Enlarge
Mosyle Manager Enlarge
Enlarge
Meraki Systems Manager 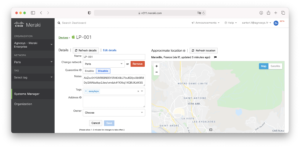 Enlarge
Enlarge
Miradore 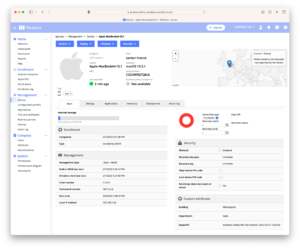 Enlarge
Enlarge
Want to know more ?
Request your invitation from the MacAdmins.org page or send us a message to receive your invitation.